As the central nervous system of a business’s cybersecurity strategy, SIEM tools help defend against all manner of attacks. Small businesses are just as likely to fall victim to a security threat as large enterprises, so it’s critical that you have sufficient measures in place to prevent malicious figures from inflicting harm on your business systems.
Some small businesses will find SIEM managed services a bit more accessible and easier to implement. On the other hand, SMBs that have advanced needs or want more control over their systems will benefit from deploying and managing a SIEM software solution themselves. In either case, SIEM technology is a major component of a fully baked cybersecurity strategy.
Jump to:
- What is SIEM?
- SIEM software vs. SIEM managed services
- SIEM software features
- How to choose a SIEM product
Top SIEM product comparison
| Vendor | Datadog Security
Monitoring |
Splunk
|
Rapid7
|
Manage Engine
|
Exabeam
|
| Customizable alerts | Yes | Yes | Yes | Yes | Yes |
| Real-time monitoring | Yes | Yes | Yes | Yes | Yes |
| Behavioral analytics | No | Yes | Yes | No | Yes |
| Threat intelligence | Yes | Yes | Yes | Yes | Yes |
| Ticketing system integration | Yes | No | Yes | Yes | No |
| Automated incident response | No | Yes | Yes | Yes | Yes |
| Compliance reporting | No | Yes | No | Yes | Yes |
| Managed service offering | No | No | Yes | No | No |
Datadog Security Monitoring: Best SIEM for integrations
4/5 stars
Pros
The biggest benefit of Datadog’s platform is its integrations with more than 400 cloud vendors, applications, and web service providers. Pretty much any component of your current development stack will integrate with Datadog straight out of the box.
It has strong customization capabilities for dashboards and reporting, and many customers say the analytics tools make monitoring system health and performance much easier. The user interface is intuitive, too, once you’ve done the work to get it up and running.
Cons
One drawback to Datadog’s security monitoring solution is the complexity that can come with configuration. Each device and integration must be set up manually, whereas this process is sometimes automated with Datadog’s competitors.
The pricing structure leaves a bit to be desired, too. Datadog wasn’t primarily designed for SIEM, so there are separate modules for security monitoring, log management, infrastructure monitoring, and network monitoring. You have to contact their sales team to understand how much it will cost to bundle more than one module.
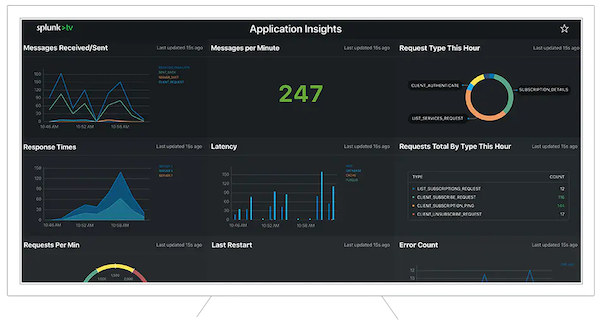
Splunk Enterprise Security: Best SIEM for advanced needs
4.5/5 stars
Pros
Splunk Enterprise Security integrates with some of the company’s other tools, including user behavior analytics (UBA), machine learning, security orchestration automation and response (SOAR). Many users laud Splunk’s flexible features and deployment modes.
With this tool, you can reduce incident response time, automate workflows, and investigate breaches more quickly and efficiently. The threat analytics capabilities help you triage alerts so you’re able to prioritize the most important notifications. Plus, Splunk offers a free 7-day sandboxing trial that lets you get a taste of the platform’s functionality first-hand.
Cons
Many users cite the licensing model as the biggest disadvantage of the platform. While Splunk is an ideal all-in-one solution for businesses with advanced needs, its capabilities come with a hefty price tag compared to other SIEM solutions. This is especially true if you have a large volume of data logs to monitor.
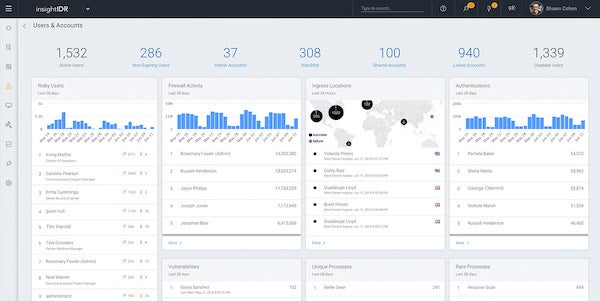
Rapid7 InsightIDR: Best value SIEM
5/5 stars
Pros
Rapid7’s InsightIDR solution offers a simple, straightforward deployment process and an intuitive user interface among other common benefits. It also has strong behavioral analytics for users and attackers alike, so you can monitor behavioral patterns from multiple perspectives.
Rapid7 is also the only SIEM vendor on this list with a managed services offering. If you’re on the fence about managing this kind of software in-house, this is a solution that can give you the benefits of SIEM software without actually needing to deploy it yourself.
Cons
Some users have reported challenges creating manual queries at times and some of the expected features of other SIEM products, like database and email monitoring, are missing with InsightIDR. Mobile access can also be a bit cumbersome, and the default reporting and alerts features can be frustrating to some users.
ManageEngine EventLog Analyzer: Best SIEM for compliance
5/5 stars
Pros
ManageEngine’s Eventlog Analyzer tool was created with auditing and compliance needs in mind. It automates log management, file/folder monitoring, and user access/activity auditing. Eventlog Analyzer includes built-in reporting templates for PCI, FISMA, CCPA, SOX, HIPAA, ISO 27001, and many other regulations.
The Eventlog Analyzer platform leans more toward the security information side of SIEM than the security events side, so it’s a great solution for managing a large volume of log sources. It also comes at a very reasonable price point with a free edition for 5 log sources that never expires.
Cons
Some users have requested a more user-friendly interface from ManageEngine, and others have reported some issues with the application’s stability and performance. The feature set is not as robust as some other SIEM providers, so you may need to look elsewhere for behavioral analytics, threat visualization, or other advanced capabilities.
Exabeam: Best SIEM for analytics
4.5/5 stars
Pros
Exabeam offers unlimited log data collection, which is ideal for meeting reporting requirements as you scale your business. Its pricing is based on users, so lean IT teams can maintain the same security posture as large enterprises from a more cost-effective price point.
Many customers have noted how easy the platform is to use once deployed. The automation features are also very thorough, which makes incident response very efficient and Exabeam’s add-on capabilities make it a strong tool for a wide range of needs. Perhaps most notably, Exabeam has exceptional behavioral analytics and automation capabilities.
Cons
Some customers have reported that Exabeam’s deployment could be simpler, so it could take a considerable amount of time and effort to get the software operational. Additionally, some users cited lack of flexibility as a major pain point.
What is SIEM?
Security information and event management (SIEM) is a category of tools that help collect and manage data across your entire company network. Sources of this data include workstations, servers, and other types of network devices. It’s traditionally deployed as on-premises software, but it can also be delivered as a cloud-based product or as a managed service.
The ultimate goal of SIEM tools is enhanced cybersecurity monitoring and prevention from all angles. Unlike its counterparts, which are restricted to solely security information management (SIM) or security event management (SEM), SIEM tools include features for detecting threats as they emerge and taking action to prevent them from causing damage.
Other categories of cybersecurity tools hone in on individual components or layers of your IT system like your network or your endpoint devices, but SIEM tools monitor the composite of all those pieces. As such, a single SIEM offering will likely include capabilities for endpoint detection and response (EDR), intrusion detection and protection (IDP), application performance monitoring (APM), and numerous other channels.
SIEM software vs. SIEM managed services
As referenced above, SIEM tools are most commonly implemented as a software solution that’s either managed on-premises or delivered as a cloud-based application.
With the first method, a company must purchase and maintain enough servers to support the software and the data it contains. Cloud-based solutions are delivered over the internet, thereby eliminating the need for advanced hardware. However, both on-premises and cloud-based solutions require enough IT staff for day-to-day operations and monitoring.
Some SMBs may be able and willing to accept the cost of investing in SIEM software as well as the manpower required to use it effectively. However, these considerations might make SIEM software a non-starter for a large portion of SMBs.
This is where SIEM managed service providers (MSPs) have an advantage. Instead of spending a lot of time and money on configuring and managing the software in-house, small and midsize businesses can leverage an MSP’s expertise and resources to achieve the same results for a monthly fee.
Related:Managed SIEM: A Faster Way to Great Security
SIEM software features
For SMBs that want to manage their SIEM tools themselves, there are a few features to consider when evaluating a specific product’s aptitude.
Core features
At its most fundamental level, SIEM software combines information and event management capabilities. Therefore, all SIEM products should include features for log collection and normalization — that is, recording and organizing data about system-wide activity — as well as event detection and response.
The consolidated data should include information from a range of sources including servers, firewalls, antivirus software, switches, routers, and endpoint devices. When the monitoring features detect an anomaly, the SIEM platform should then analyze the threats in real time and take appropriate actions to prevent damage.
These two sides of security management will help you monitor your network from all angles at all times and dig into the finer details of unexpected activity when needed.
Advanced features
You’ll find that some SIEM tools offer unique features that others do not. These include notifications and alerts that you can fine-tune to your preferences for the number of alerts you receive, how each notification is escalated, and any automated responses that are relevant. Similarly, a strong SIEM platform will have customizable workflows and dashboards that help you visualize your system activity and take necessary actions when a threat emerges.
Some SIEM platforms offer support for a ticketing system, so users can report problems and admins can track related events. If compliance is a top priority for your organization, some solutions also include features for compliance with HIPAA, PCI, and other regulations.
Related: Data Protection Compliance: Frameworks for Small Businesses
How to choose a SIEM product
To pick the right SIEM solution for you, start by reviewing your functionality requirements, the capabilities of your internal team, and your budget. Some solutions may fall short of the features you want or may be too expensive or complex, but you should be able to find one that meets most of your needs.
Once you’ve eliminated the non-options, explore customer testimonials and consider testing your top picks during a free trial or demo to narrow your search. A top contender will have the right balance of features, affordability, and user friendliness.
SIEM software provides tools for SMB cybersecurity
SIEM software is usually a cybersecurity tool reserved for large enterprises. It’s expensive to deploy and manage, and it usually requires a large team of IT personnel to keep it up and running. For this reason, most SMBs will have their SIEM needs met more economically with a managed service. However, SMBs that are able to meet the hardware, software, and staffing demands will be able to maintain a strong cybersecurity posture and prevent threats from causing significant damage.
Read next: 10 Basic Cybersecurity Practices Every Small Business Owner Should Know